Published on: May 3, 2024
NIS 2.0 Directive: Key Changes and Deadlines
NIS 2.0 Directive marks a significant shift in the European Union's approach to cybersecurity, expanding its scope and enhancing measures to protect essential services and digital infrastructure.
This article breaks down the critical updates, compliance requirements, and strategies to strengthen your cybersecurity posture, helping your organization adapt and thrive.
Let's get started!
What is the NIS 2.0 Directive?
NIS 2.0 Directive, or the Network and Information Systems Directive 2.0, is an update from the original NIS 1.0. Issued by the European Union, it aims to improve the security of networks and information systems within critical sectors. The main purpose of this directive is to strengthen cybersecurity resilience and maintain the smooth operation of vital services across the EU.
What is The Difference Between NIS 1.0 and NIS 2.0?
The original NIS 1.0 Directive introduced essential cybersecurity measures for key service operators and digital service providers. However, with the rise of more sophisticated and frequent cyber threats, there was a pressing need for a stronger regulatory framework. NIS 2.0 expands on its predecessor, enhancing measures to better tackle new and emerging cybersecurity challenges.
Core Objectives
NIS 2.0 focuses on several key goals to enhance cybersecurity across the EU:
1. Enhanced Coverage: NIS 2.0 now includes more entities under the directive, covering a wider range of essential sectors and services to ensure comprehensive protection.
2. Improved Resilience: NIS 2.0 introduces stricter cybersecurity protocols to bolster the resilience of vital services and digital infrastructures against cyber threats.
3. Streamlined Cooperation: It encourages better coordination and information sharing among EU countries, aiming for a unified approach to managing cyber incidents.
Motivation for Transitioning to NIS 2.0
Several factors drove the upgrade from NIS 1.0 to NIS 2.0, emphasizing the need for stronger cybersecurity measures, here are some reasons:
1. Emerging Threat Landscape:The increasing frequency of cyber threats like ransomware and data breaches needs a more dynamic and fortified cybersecurity strategy.
2. Technological Advancements: Developments in technology, such as cloud services, the Internet of Things (IoT), and Artificial Intelligence (AI), have broadened the potential attack areas, calling for updated regulations.
3. Global Regulatory Trends: As global regulations on cybersecurity become more stringent, the EU needed to update its own measures to stay aligned with international standards.
These driving forces made it essential for the EU to adopt NIS 2.0, ensuring that its cybersecurity framework can effectively respond to current and future challenges.
Scope and Applicability
So, who does the NIS 2.0 Directive affect?
This updated version extends beyond just the primary operators of essential services (OES) and digital service providers (DSPs). Now, it covers a variety of sectors such as healthcare, water, energy, transport, and digital infrastructure.
This is the cool part:
Small to medium-sized enterprises (SMEs), which play a pivotal role in the ecosystem, are also included under this directive due to the increasing cybersecurity threats they encounter.
If your business is part of these sectors, adhering to the NIS 2.0 requirements is crucial, not just for compliance, but for enhancing your cybersecurity defences.
Geographical Reach
The directive applies throughout the European Union, impacting all member states. Interestingly, it also affects non-EU businesses operating within the EU. This means that any company, regardless of its headquarters' location, must comply with the NIS 2.0 standards if it operates in the EU.
This broad jurisdiction highlights the EU's dedication to improving cybersecurity and ensuring a safe digital landscape for every business operating under its jurisdiction. Compliance is essential for both local and international companies.
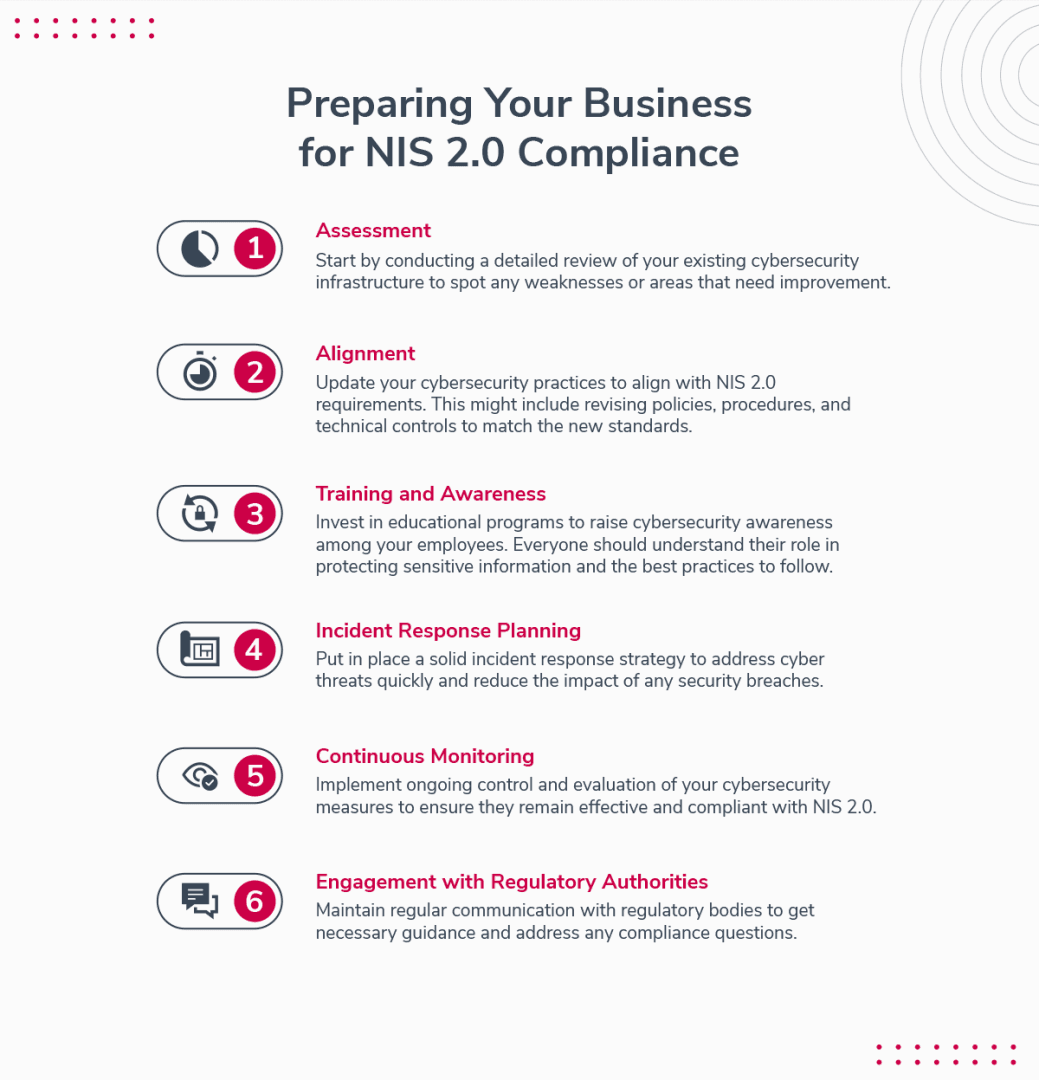
Preparing Your Business for NIS 2.0 Compliance
Getting your business ready for NIS 2.0 compliance involves a clear and structured approach. Here's how you can ensure you meet the directive's standards:
Assessment: Start by conducting a detailed review of your existing cybersecurity infrastructure to spot any weaknesses or areas that need improvement.
Alignment: Update your cybersecurity practices to align with NIS 2.0 requirements. This might include revising policies, procedures, and technical controls to match the new standards.
Training and Awareness: Invest in educational programs to raise cybersecurity awareness among your employees. Everyone should understand their role in protecting sensitive information and the best practices to follow.
Incident Response Planning: Put in place a solid incident response strategy to address cyber threats quickly and reduce the impact of any security breaches.
Continuous Monitoring: Implement ongoing control and evaluation of your cybersecurity measures to ensure they remain effective and compliant with NIS 2.0.
Engagement with Regulatory Authorities: Maintain regular communication with regulatory bodies to get necessary guidance and address any compliance questions.
By following this roadmap, you can streamline your compliance process and enhance your defences against cyber threats.
Remember, maintaining cybersecurity is an ongoing process that requires constant vigilance and adaptation.
Security and Incident Reporting: Protecting Your Operations
NIS 2.0 includes a solid framework designed to strengthen cybersecurity defences and ensure prompt incident reporting. Let's break down the essentials:
Risk Management:
A key aspect of NIS 2.0 is effective risk management. This involves identifying, evaluating, and mitigating cybersecurity risks that could threaten the security and integrity of essential services.
By conducting thorough risk assessments, businesses can proactively address vulnerabilities and boost their overall security stance.
Incident Reporting
Quick and efficient incident reporting is a crucial element of cybersecurity resilience. NIS 2.0 requires that operators of essential services and digital service providers report any significant incidents that might disrupt vital services or digital services.
This includes incidents such as cyberattacks, system failures, and data breaches. Moreover, timely reporting enables quick responses and mitigation efforts, reducing the impact on operations and stakeholders.
Significance
Robust risk management and incident reporting are essential for protecting business operations, safeguarding sensitive data, and maintaining trust among customers and stakeholders.
Additionally, proactive risk management and reporting show a commitment to cybersecurity, enhancing a business's reputation and credibility in the market.
Enforcement and Penalties: Navigating Compliance Challenges of NIS 2.0
Understanding the potential consequences of non-compliance with NIS 2.0 is essential. Here's what you need to know:
Potential Fines
Non-compliance can lead to substantial financial penalties. National authorities can impose fines on essential service operators and digital service providers that fail to meet the directive's requirements.
The severity of the fine depends on the nature of the breach and its impact on essential services or digital infrastructure.
Essential entities, such as those in the healthcare and energy sectors, can face fines of up to €10,000,000 or 2% of their total annual worldwide turnover, whichever is higher.
Digital service providers and other important entities, such as those in manufacturing and research, face fines of up to €7,000,000 or 1.4% of their annual turnover, whichever is higher.

Role of National Authorities
National authorities are crucial for enforcing NIS 2.0. They monitor compliance, investigate incidents, and impose penalties when necessary. Additionally, they guide businesses to improve their cybersecurity measures and ensure compliance.
Importance of Compliance
Given the financial and reputational risks associated with non-compliance, adhering to NIS 2.0 is a legal necessity and a strategic priority. By prioritizing cybersecurity compliance, businesses can mitigate risk, protect sensitive data, and maintain the continuity of essential services, ensuring long-term stability and resilience.
NIS 2.0 Directive Implementation and Compliance
Critical Deadlines
One of the first things businesses need to know is the timeline for compliance with the NIS 2.0 Directive. Member states must incorporate the directive into their national law by 17 October 2024, with the laws taking effect on 18 October 2024.
Enforcement will begin on 17 January 2025. Therefore, businesses need to act quickly to meet these deadlines and avoid potential penalties for non-compliance.
Meeting the compliance deadlines for NIS 2.0 is crucial, but it is only the beginning. To ensure sustained cybersecurity resilience and avoid potential penalties, businesses must adopt a proactive and strategic approach to NIS 2.0 compliance.
NIS 2.0: Steps Towards Compliance
Achieving compliance with the NIS 2.0 Directive involves a structured approach and careful planning.
Here's a step-by-step guide to help you navigate the compliance process:
Conduct Risk Assessments: Start by thoroughly assessing your organization's infrastructure, systems, and services. Specifically, identify potential threats, vulnerabilities, and the impact of cyber incidents on your operations.
Establish Incident Response Strategies: Develop incident response plans specific to your organization's needs. In particular, you have to define roles and responsibilities, set up communication channels, and implement procedures for detecting, responding to, and recovering from cyber incidents.
Enhance Security Measures: Introduce appropriate technical and organizational measures to address identified risks and strengthen your cybersecurity posture. Particularly, this might include encryption, access controls, network segmentation, and regular security updates.
Ensure Continuous Monitoring and Review: Since cyber threats constantly evolve, it's crucial to regularly update and review your cybersecurity measures. Implement systems to monitor your networks continuously to promptly detect and address new threats.
Challenges in Harmonization
The NIS 2.0 Directive seeks to standardize cybersecurity requirements across the EU, but achieving consistent compliance faces some challenges:
Differences in National Legal Frameworks: The directive must be transposed into national law by each member state, which can lead to differences in implementation and interpretation.
Varying Interpretations: Different member states and sectors may interpret the directive's requirements differently, potentially causing inconsistencies.
Cybersecurity Maturity: The cybersecurity maturity of various sectors and member states varies, making it challenging to ensure a uniform level of compliance.
To navigate these challenges effectively, you can:
Stay Informed: Regularly review updates and guidance from regulatory bodies and industry associations to stay compliant with evolving requirements.
Engage with Stakeholders: Collaborate with peers, industry groups, and regulatory bodies to share best practices and address common issues.
Adopt a Risk-Based Approach: Tailor cybersecurity measures to your organization's specific risk profile and operational context, considering sector-specific requirements and regulatory expectations.
By adopting a proactive and collaborative approach, businesses can overcome these harmonization challenges and align their cybersecurity measures with NIS 2.0.
Beyond Compliance: Strengthening Cybersecurity Posture
NIS 2.0 is more than just a set of regulations to be followed; it presents an opportunity for organizations to enhance their overall cybersecurity strategy. By embracing this directive with a proactive mindset, organizations can revamp their cybersecurity strategies, aligning them with industry best practices and evolving threats.
A key aspect of this approach is fostering a culture of cybersecurity awareness at all levels of the organization. This includes implementing technical measures and educating employees on cybersecurity hygiene and their role in protecting digital assets. In addition, training programs, simulated phishing exercises, and regular awareness campaigns can help create a cyber-resilient workforce.
Additionally, organizations should integrate cybersecurity into their broader business strategy. Cybersecurity should not be treated as an afterthought or a separate function but as a core part of every operation - from product development to customer service. This holistic approach embeds security into the organization's foundation, rather than treating it as an add-on.
Talking about a holistic approach, check out our all-in-one GRC platform here.
Leveraging Technology and Partnerships
Cybersecurity is constantly evolving, making collaborations and partnerships extremely valuable. By building strategic partnerships with technology vendors, industry peers, and cybersecurity experts, organizations can share resources, threat intelligence, and expertise to better manage risks.
Technology as a Force Multiplier: Investing in advanced cybersecurity technology can greatly support NIS 2.0 compliance. Threat detection systems and encryption protocols offer a strong foundation for resilience, while automation tools help reduce human error and ensure consistent compliance processes.
Cloud-Based Solutions: Cloud solutions provide scalability and flexibility, helping organizations adapt to changing regulatory needs and evolving threats. Migrating essential infrastructure and data to secure cloud environments can enhance agility while mitigating risks associated with on-premises systems.
Final Thoughts
The NIS 2.0 Directive represents a significant milestone in the ongoing effort to strengthen cybersecurity across the European Union. By understanding the key provisions and requirements of the directive, businesses can navigate compliance challenges more effectively. Moreover, it enhances their cybersecurity readiness.
By prioritizing risk management, incident reporting, and compliance with NIS 2.0, businesses can boost their defences, mitigate risk, and protect their operations in an increasingly digital world.
StandardFusion offers a comprehensive platform that streamlines compliance and risk management, providing an integrated approach to GRC that simplifies adherence to NIS 2.0.
With centralized data, automated workflows, and holistic risk assessment tools, StandardFusion enables businesses to enhance cybersecurity, ensuring a proactive and resilient digital presence across the EU.
Do you need help? Connect with our team and book a demo to see StandardFusion in action.







