Published on: Nov 8, 2022
Everything You Need To Know About The ISO 27001:2022 Update
The ISO 27001:2022 update was finally published this past October 25, 2022. So, if you are wondering what this means to you and your organization, we got your back!
This article will cover the main changes in the Mandatory Clauses, Annex A, and how to transition to the new ISO 27001:2022 update.
Also, if you need an in-depth review of the standard, check out our 8-part Guide to ISO 27001.
Let's dive right in!
ISO 27001 - Quick Overview
Technology has rapidly changed how people work in the past 20 years. Back then, less than 7% of the world was online, not even half of Americans had broadband access at home, social media was far from becoming a hot topic, and ISO 27001 didn't even exist.
The first edition of the internationally recognized information security standard was published in 2005. Then, it wasn't until 2013 that the International Standards Organization (ISO) reviewed the set of controls and issued a second revision.
Now, we are dealing with the third revision, and we expect further changes to happen much faster as cybersecurity threats grow exponentially.
ISO 27001:2022 Challenges
The ISO 27001:2022 update has much more significant challenges when trying to maintain its current requirements.
Organizing a set of comprehensive controls to cover all potential security, cybersecurity, and privacy obligations is hard. However, writing it in a way that is simple enough to fit approximately 30 pages is even more complicated. Generally, the reviewers do a good job when simplifying the standard.
Simplification is critical if the intention is to have more companies adopt 27001 as a baseline for their security controls. With more adherents, ISO 27001 leads the InfoSec compliance world and becomes a must-have for anyone trying to sell technology.
In the B2B space, customers won't take less than an ISO 27001-certified product.
There is no question about the value of ISO certification. Nevertheless, for anyone looking forward to implementing this standard or transitioning from the previous version, there are key changes that require some planning.
The New Changes of ISO 27001:2022
Mandatory Clauses
There aren't many significant changes there, but a few that deserve comments:
4.4 Information security management system - This new clause requires that processes and "their interactions" are identified, which reminds us a lot of ISO 9001. Therefore, you can design interactions as part of diagrams and flow chats.
Several clauses and notes make it clear that the Annex A controls are not exhaustive. You should use them as a baseline. However, all organizations should look at their environments to correctly identify any other necessary control, risks, etc.
6.2 Information Security objectives. Objectives must be documented and available for all stakeholders.
6.3 Planning of changes. From now on, all changes require documented planning.
8.1 Operational planning and control. Organizations must define a criteria for operational processes. However, a criteria can be a broad term, from a security requirement to a business need or customer request.
9 Performance evaluation. Methods to evaluate and monitor your controls should produce comparable results so the organization can assess trends.
9.2 Internal audits. Internal assessments must cover all organizations' requirements, not only ISO 27001. This may be a broader attempt to be more comprehensive as a Management System.
Annex A
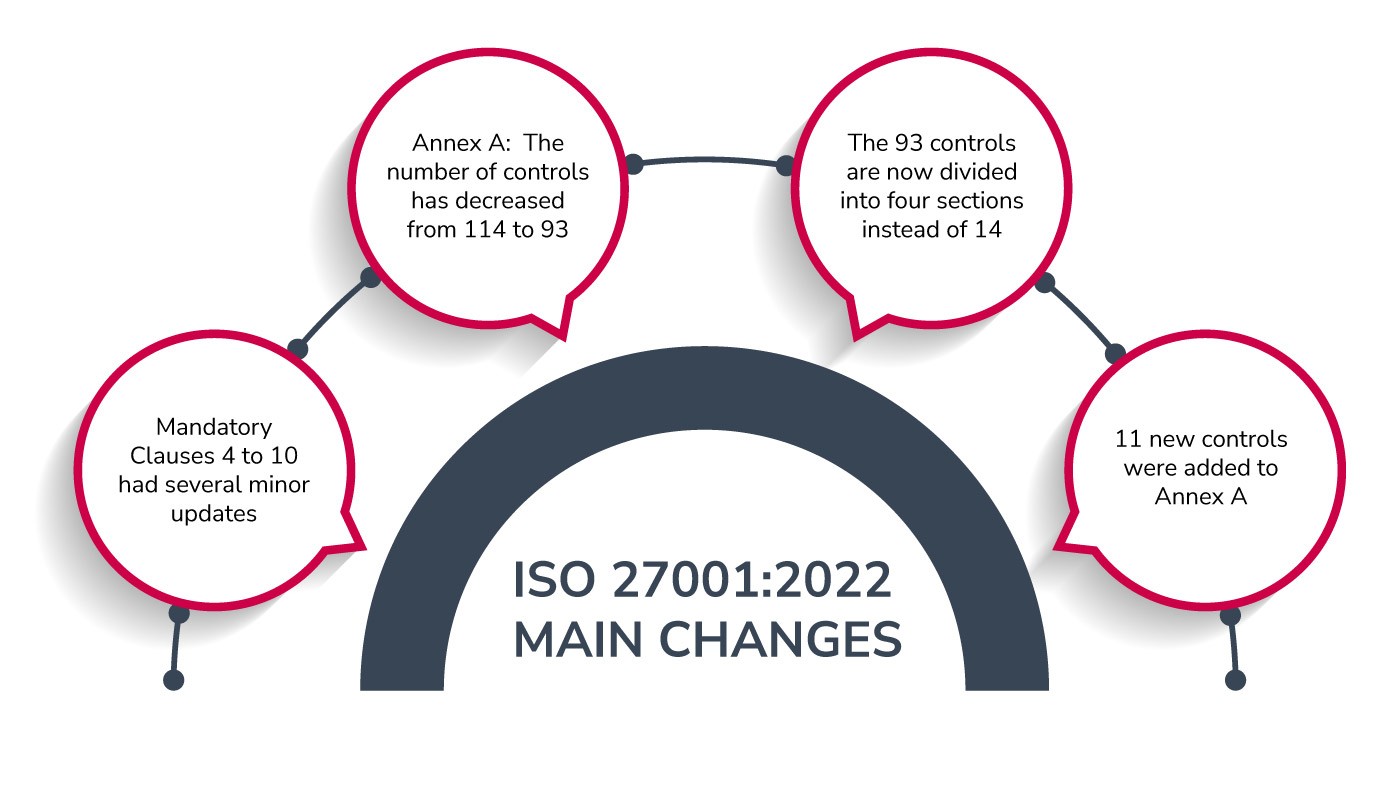
Annex A has seen the greatest change. The updated version of ISO 27001 Annex A has been completely restructured and revised. As a result, the number of controls has decreased from 114 to 93 in the new version of ISO 27001. Also, these security controls are now divided into four sections instead of the previous 14.
Furthermore, this change represents a tangible attempt to make the standard more concise and simpler to implement. The overlaps and repetitions have been eliminated to create five major security attributes that make them easier to group.
The new Sections and Controls of ISO 27002:2022 are:
Section 5: Organizational (37 controls)
Section 6: People (8 controls)
Section 7: Physical (14 controls)
Section 8: Technology (34 controls)
In summary, 35 controls remained unchanged, 23 controls were renamed, 57 controls were merged to form 24 controls, and 11 new controls were added:
5.23 Information security for use of cloud services
5.30 ICT readiness for business continuity
5.7 Threat Intelligence
7.4 Physical security monitoring
8.1 Data masking
8.9 Configuration management
8.10 Information deletion
8.12 Data leakage prevention
8.16 Monitoring activities
8.23 Web filtering
8.28 Secure coding
How Will The Update Affect Your Organization if You Are Implementing ISO 27001?
First of all, don't panic. Certification entities will likely offer certification to ISO 27001:2022 just six months after its publication. Also, ISO 27001:2013 will be retained for another three years, so all your work to implement 27001:2013 will still be worth it.
However, you might want to use the new Annex A controls from ISO 27001:2022 as an alternative control set, depending on the progress of your ISO 27001:2013 implementation project. If you want to do this, you will still need to compare the new controls with the 2013 Annex A controls in your Statement of Applicability.
How Will The Update Affect Your Organization if You Are Already Certified to ISO 27001:2013?
Remember, you will have time ("Transition Period") to fully migrate to the new requirements. However, the best moment to do that is before your next internal audit, no matter if you have been certified for years or even if you are in the process of certification.
The internal ISO 27001 audit involves a detailed assessment of your organization's ISMS to ensure it complies with the standard's criteria. That would allow you to evaluate if you deployed the changes correctly without putting the certification at risk.
Another critical decision would be allocating the internal audit activities, at least, three months before the external assessment. This timeline would allow you to identify any potential nonconformities and fix those before the external assessor comes in.
Not sure how to start?
Connect with StandardFusion's team to help you overcome your ISO and GRC challenges. Also, you can check out this guide, complying with the changes to ISO 27001:2022, if you need more help transitioning to the updated standard.
What can GRC do for you?
A powerful GRC platform can be your best friend when mapping controls across your organization, identifying potential risks, and allocating ownership. Moreover, the software allows a centralized approach to information security as a "management system," exactly how the new standard suggests.
Also, you can integrate records, allowing you to visualize and understand the interaction between processes, the creation of workflows and rapidly visualizing these interconnections will also streamline your transition.
Key takeaways
Although the last ISO 27001 update was almost 10 years ago, we expect further changes to happen much faster as cybersecurity threats keep growing exponentially.
Following, are some of the most significant ISO 27001:2022 updates:
Mandatory Clauses
4.4 Information security management system
Several clauses and notes make it clear that the Annex A controls are not exhaustive
6.2 Information Security objectives
6.3 Planning of changes
8.1 Operational planning and control
9 Performance evaluation
9.2 Internal audits
Annex A
The main changes include: 35 controls remained unchanged, 23 controls were renamed, 57 controls were merged to form 24 controls, and 11 new controls were added.
Remember, you will have time ("Transition Period") to fully migrate to the new requirements. The best moment to do that is before your next internal audit. It doesn't matter if you have been certified for years or are in the process of certification.
Smooth Transition
Lastly, GRC software can help you transition smoothly to ISO 27001:2022 by mapping controls across your organization, identifying potential risks, and allocating ownership. Moreover, GRC tools like StandardFusion allow you to build a centralized approach to information security as a "management system," precisely as the new standard suggests.







